Khatam University Amphitheater
2.000.000 Tomans
(Scholarships are available for candidates with relevant research background evidenced by their CV)
August 5, 2022
Deadline Extended to August 12
Mohammad Morovati
- Mohammad Reza Mousavi
- Hossein Hojjat
Fereshte Allahverdi
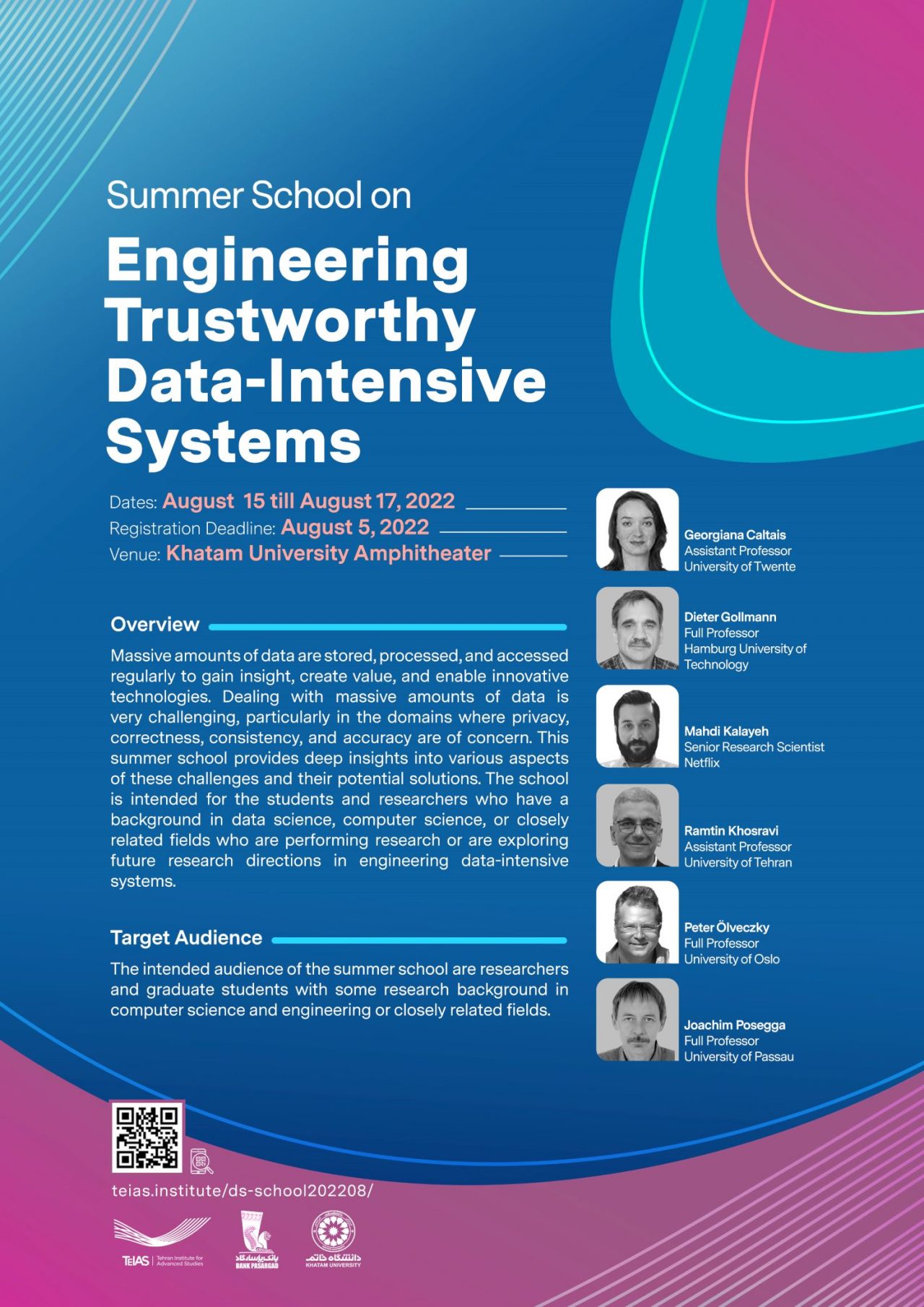
Overview
Massive amounts of data are stored, processed, and accessed regularly to gain insight, create value, and enable innovative technologies. Dealing with massive amounts of data is very challenging, particularly in the domains where privacy, correctness, consistency, and accuracy are of concern. This summer school provides deep insights into various aspects of these challenges and their potential solutions. The school is intended for the students and researchers who have a background in data science, computer science, or closely related fields who are performing research or are exploring future research directions in engineering data-intensive systems.
Target Audience
The intended audience of the summer school are researchers and graduate students with some research background in computer science and engineering or closely related fields.
Poster Session
During the summer school there will be a poster session for attendees to present their ongoing projects. Posters must be in English, A1 size (in portrait orientation). A PDF version of the poster must be submitted by July 5 as part of the online registration process. The summer school scientific committee selects a number of posters for presentation and notifies the authors on July 8. The selected posters must be printed beforehand and brought along by the author on the first day of the school (July 11). The winner of the best poster award will be announced at the closing ceremony.
Speakers

Georgiana Caltais
Assistant Professor
University of Twente
Title: DyNetKAT: An Algebra of Dynamic Networks
Abstract. In this talk I will introduce DyNetKAT -a formal language for specifying dynamic updates for Software Defined Networks. The latter can play an important role in solving issues concerning big data applications, including data processing in cloud data centers, optimisations and data delivery. DyNetKAT builds upon Network Kleene Algebra with Tests (NetKAT) and adds constructs for synchronisations and multi-packet behaviour to capture the interaction between the control- and data plane in dynamic updates. A sound and ground-complete axiomatisation of DyNetKAT will be discussed, together with an efficient method for reasoning about safety properties, and associated case studies.
Title: Causal Reasoning in Systems
Abstract. Causal inference plays an important role in assessing why did a hazardous situation occur and how certain undesired scenarios could have been avoided, or when performing fault localisation in systems, amongst others. In this talk I will introduce a notion of “actual causality”, proposed by Joseph Halpern and Judea Pearl in their seminal work “Causes and explanations: A structural-model approach”. An adoption to the setting of transition systems and, implicitly, DyNetKAT models, will be discussed as well. As we shall see, causal inference for DyNetKAT enables addressing interesting questions such as Reachability: “Can host A communicate with host B? Can every host communicate with every other host?”, or Security: “Does all untrusted traffic pass through the intrusion detection system located at C?”.

Dieter Gollmann
Full Professor
Hamburg University of Technology
Title: The Hitchhiker’s Guide to Cybersecurity
Abstract. The talk will link the evolution of cybersecurity to the developments in IT systems and their applications over the past fifty years. It will explain when and why new concepts in cybersecurity emerged, and point to two pitfalls faced by students joining this field. Fashionable new terms enter the trade and research literature, creating the illusion of completely new challenges in contrast to imaginary traditional solutions, while in fact just relabelling established concepts. On the other hand, established concepts can create a blinkered view of the world that keeps applying old solutions to genuinely new security challenges.
Title: Blockchain – Facts & Fiction
Abstract. Blockchains have greatly agitated the public and the research community in recent years. This talk will highlight the major technical innovations in the Bitcoin blockchain, show how the term ‘blockchain’ has then evolved and been applied to systems fundamentally different from the Bitcoin blockchain, and examine which of the popular claims about blockchains stand up to a critical analysis. The talk will also give an overview of open questions in blockchain research, and discuss the challenges faced when conducting research in a field driven by a buzzword.

Mahdi Kalayeh
Senior Research Scientist
Netflix
Title: A Journey Toward Video Understanding with Minimal Labels

Ramtin Khosravi
Assistant Professor
University of Tehran
Title: Learning Behavioral Models of Software Product Lines

Peter Ölveczky
Full Professor
University of Oslo
Title: Formal Specification and Analysis of Distributed Systems using Maude
Abstract. Rewriting logic is a powerful and general, yet simple and intuitive, logic for specifying dynamic systems, and is particularly suitable to specify distributed computer systems in an object-oriented style.
Maude is a programming/modeling language and high-performance analysis tool for rewriting logic. Data types are defined by equational specifications (which operationally can be seen as rich term rewrite systems), while dynamic behaviors are specified by (possibly conditional) rewrite rules. Maude models can then be subjected to: simulation by rewriting; reachability analysis by search; temporal logic model checking; and various forms of theorem proving using associated tools.
Maude has been successfully applied to a wide range of sophisticated systems, including: transport protocols, cloud-based distributed transaction systems, biological systems, human cognition, programming and modeling language semantics and analysis, electronic contracts, cyber-physical systems, and so on.
This talk gives an introduction to specification and analysis in Maude. It also briefly touches upon some applications of Maude, and extensions to real-time and probabilistic systems.
Title: Design and Validation of Cloud Storage Systems using Maude
Abstract. Today’s large cloud-based applications (e.g., Gmail, Telegram, etc.) store and manipulate enormous amounts of data, that, furthermore, must be available all the time. In addition, such applications must be both correct and have high performance.
To deal with large amounts of data while offering high availability and throughput and low latency, cloud computing systems rely on distributed, partitioned, and replicated data stores. Such cloud storage systems are complex software artifacts that are very hard to design, analyze, and implement.
I argue that Maude, together with a statistical model checker such as PVeStA, should be a suitable tool to model and formally analyze both the correctness and the performance of complex cloud storage designs early in the development process. This is not only useful to arrive at correct designs, but also to very early compare the expected performance of different design choices.
I give an overview of the application of Maude to a wide range of state-of-the-art cloud transaction systems, such as Apache Cassandra, Google’s Megastore, UC Berkeley’s RAMP transactions, and variations of these. I discuss how the model-based performance estimates relate to real implementations, and also how a correct design can be automatically transformed into a correct-by-construction distributed implementation that can execute real workloads (e.g., YCSB workloads).
Finally, I briefly summarize the experiences of the use of a different formal method for similar purposes by engineers at Amazon Web Services.

Joachim Posegga
Full Professor
University of Passau
Title: Higher Education and Academic Research in Germany: Structures and Practice
Abstract. The German approach to organising universities and research funding is fundamentally different from the Anglo-Saxon or French system. Rather than following a centralised approach, Germany organised its academic system in a decentralised manor tight to its 16 geographic regions („Länder“). We will explain this structure with an emphasis on technical fields like Computer Science.
The talk will firstly introduce the governance structures German universities are embedded in; these are based on the idea of regional responsibility for teaching, and a mix of regional and centralised funding for research. There is also a large variety of schemes for a university-internal organisation, which we will discuss exemplified at the situation in Bavaria.
Research itself is often carried out in cooperative projects, mostly granted through competitive application procedures. We present the major funding organisations and their strategic setting. The talk ends with an outline of a recently acquired project “ForDaySec”, a combine of five Bavarian Universities carrying out basic research on IoT-Security.
Schedule
08:00 – 08:30 Reception and light refreshment
08:30 – 09:00 Opening
09:00 – 09:30 Coffee / Tea Break
09:30 – 11:00 TBA (Design for Scalability and Dependability: From Theory to Practice)
11:00 – 11:30 Coffee / Tea Break
11:30 – 12:30 Georgiana Caltais (DyNetKAT: An Algebra of Dynamic Networks)
12:30 – 13:30 Lunch
13:30 – 15:00 Georgiana Caltais (Causal Reasoning in Systems)
15:00 – 16:30 Round-table: Rigorous Design of Data-Intensive Systems
08:30 – 09:00 Light refreshment
09:00 – 10:00 Ramtin Khosravi (Learning Behavioral Models of Software Product Lines)
10:00 – 10:30 Coffee / Tea Break
10:30 – 11:30 Dieter Gollman (Online) (The Hitchhiker’s Guide to Cybersecurity)
11:30 – 12:00 Coffee / Tea Break
12:00 – 13:00 Peter Olveczky (Online) (Formal Specification and Analysis of Distributed Systems using Maude)
13:00 – 14:00 Lunch
14:00 – 15:30 Round-table: Rigorous Design of Data-Intensive Systems
15:30 – 17:30 Social Event
08:30 – 09:00 Light refreshment
09:00 – 10:00 Mahdi Kalayeh (A Journey Toward Video Understanding with Minimal Labels)
10:00 – 10:30 Coffee / Tea Break
10:30 – 11:30 Peter Olveczky (Online) (Design and Validation of Cloud Storage Systems using Maude)
11:30 – 12:00 Coffee / Tea Break
12:00 – 13:00 Dieter Gollman (Online) (Blockchain – Facts & Fiction)
13:00 – 14:00 Lunch
14:00 – 15:00 Joachim Posegga (Higher Education and Academic Research in Germany: Structures and Practice)
15:00 – 16:30 Round-table: Data Science and the University of the Future
08:00 – 08:30 Reception and light refreshment
08:30 – 09:00 Opening
09:00 – 09:30 Coffee / Tea Break
09:30 – 11:00 TBA (Design for Scalability and Dependability: From Theory to Practice)
11:00 – 11:30 Coffee / Tea Break
11:30 – 12:30 Georgiana Caltais (DyNetKAT: An Algebra of Dynamic Networks)
12:30 – 13:30 Lunch
13:30 – 15:00 Georgiana Caltais (Causal Reasoning in Systems)
15:00 – 16:30 Round-table: Rigorous Design of Data-Intensive Systems
08:30 – 09:00 Light refreshment
09:00 – 10:00 Ramtin Khosravi (Learning Behavioral Models of Software Product Lines)
10:00 – 10:30 Coffee / Tea Break
10:30 – 11:30 Dieter Gollman (Online) (The Hitchhiker’s Guide to Cybersecurity)
11:30 – 12:00 Coffee / Tea Break
12:00 – 13:00 Peter Olveczky (Online) (Formal Specification and Analysis of Distributed Systems using Maude)
13:00 – 14:00 Lunch
14:00 – 15:30 Round-table: Rigorous Design of Data-Intensive Systems
15:30 – 17:30 Social Event
08:30 – 09:00 Light refreshment
09:00 – 10:00 Mahdi Kalayeh (A Journey Toward Video Understanding with Minimal Labels)
10:00 – 10:30 Coffee / Tea Break
10:30 – 11:30 Peter Olveczky (Online) (Design and Validation of Cloud Storage Systems using Maude)
11:30 – 12:00 Coffee / Tea Break
12:00 – 13:00 Dieter Gollman (Online) (Blockchain – Facts & Fiction)
13:00 – 14:00 Lunch
14:00 – 15:00 Joachim Posegga (Higher Education and Academic Research in Germany: Structures and Practice)
15:00 – 16:30 Round-table: Data Science and the University of the Future
