Amphitheater
1.000.000 Tomans
(Waived for graduate students with good standing.)
July 31, 2023 (9 Mordad 1402)
Mohammad Morovati
- Mohammad Reza Mousavi
- Hossein Hojjat
Fereshte Allahverdi
Executive Chair
Fereshte Allahverdi
Scientific Chair
Sahber Ahmadi-Renani
Organization Chair
Amin Hamzehali
Overview
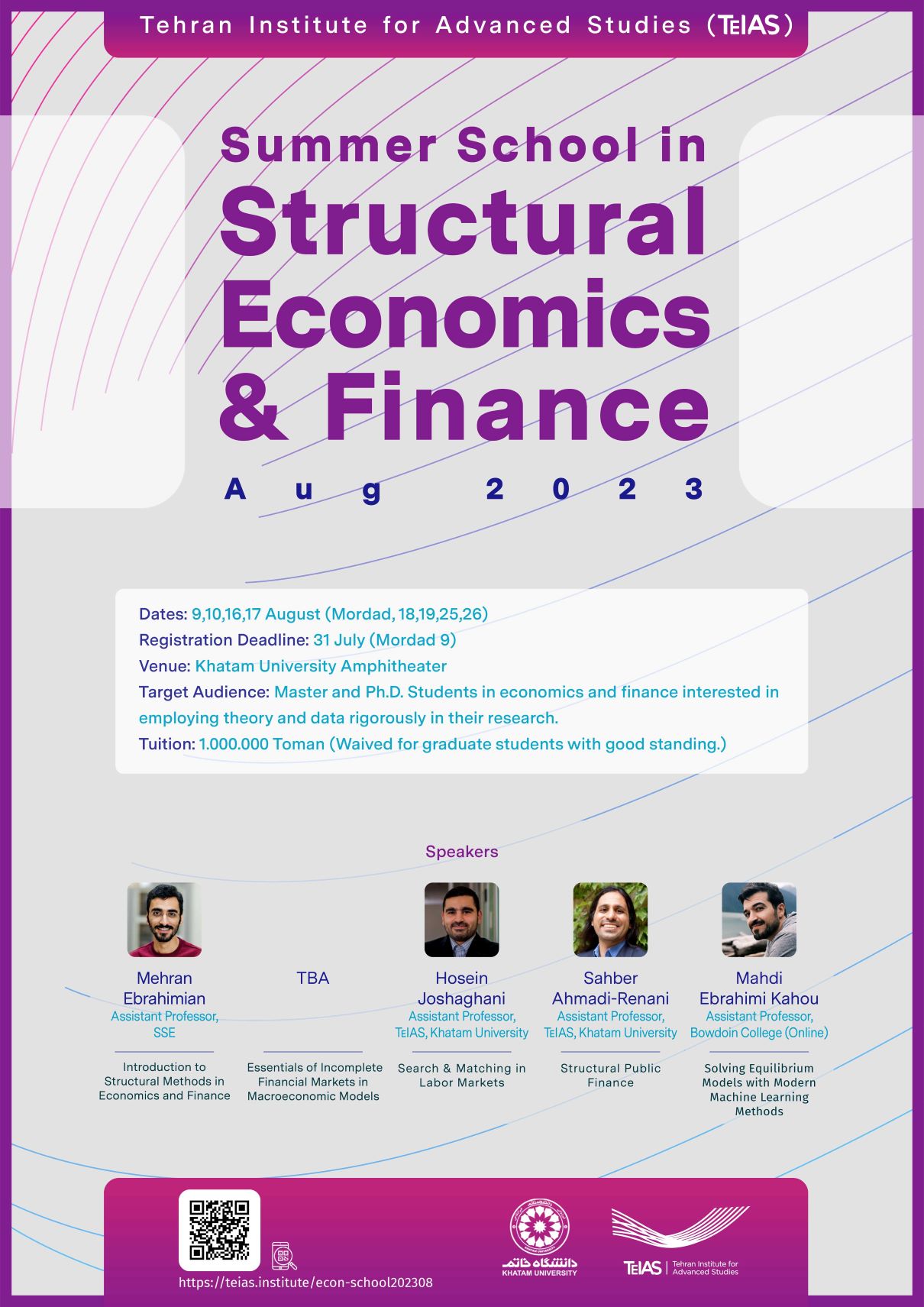
Structural models are an integral part of empirical analysis in economics and finance. Structural models offer a unique way to understand data, analyze mechanisms, and evaluate policy counterfactuals. With innovations in big data, computational tools, and numerical methods, their applications are only growing. In this summer school, we review the basics of identification and estimation of structural models along with various areas of economics and finance that benefit from the use of structural methods, such as interbank lending markets, unemployment, and family taxation.
Target Audience
Master and Ph.D. Students in economics and finance interested in employing theory and data rigorously in their research.
Speakers

Mehran Ebrahimian
Assistant Professor
SSE
TBA
Title: DyNetKAT: An Algebra of Dynamic Networks
Abstract. In this talk I will introduce DyNetKAT -a formal language for specifying dynamic updates for Software Defined Networks. The latter can play an important role in solving issues concerning big data applications, including data processing in cloud data centers, optimisations and data delivery. DyNetKAT builds upon Network Kleene Algebra with Tests (NetKAT) and adds constructs for synchronisations and multi-packet behaviour to capture the interaction between the control- and data plane in dynamic updates. A sound and ground-complete axiomatisation of DyNetKAT will be discussed, together with an efficient method for reasoning about safety properties, and associated case studies.
Title: Causal Reasoning in Systems
Abstract. Causal inference plays an important role in assessing why did a hazardous situation occur and how certain undesired scenarios could have been avoided, or when performing fault localisation in systems, amongst others. In this talk I will introduce a notion of “actual causality”, proposed by Joseph Halpern and Judea Pearl in their seminal work “Causes and explanations: A structural-model approach”. An adoption to the setting of transition systems and, implicitly, DyNetKAT models, will be discussed as well. As we shall see, causal inference for DyNetKAT enables addressing interesting questions such as Reachability: “Can host A communicate with host B? Can every host communicate with every other host?”, or Security: “Does all untrusted traffic pass through the intrusion detection system located at C?”.

Hosein Joshaghani
Assistant Professor
TeIAS

Sahber Ahmadi-Renani
Assistant Professor
TeIAS

Mahdi Ebrahimi Kahou
Assistant Professor
Bowdoin College (Online)
Schedule
1:00-3:00 & 3:30-5:30 Introduction to Structural Methods in Economics and Finance
Mehran Ebrahimian
9:00-11:00 Essentials of Incomplete Financial Markets in Macroeconomic Models
TBA
11:00-1:00
Launch and Break
1:00-3:00 Essentials of Incomplete Financial Markets in Macroeconomic Models
TBA
9:00-11:00 Search and Matching in Labor Markets
Hosein Joshaghani
11:00-1:00
Launch and Break
1:00-3:00 Search and Matching in Labor Markets
Hosein Joshaghani
9:00-11:00 Structural Public Finance
Sahber Ahmadi-Renani
11:00-1:00
Launch and Break
1:00-3:00 Structural Public Finance
Sahber Ahmadi-Renani
3:30-5:30 Solving Equilibrium Models with Modern Machine Learning Methods
Mehdi Ebrahimi Kahou
